I briefly touched on this topic already, but I guess on Yellow-Bricks the primary focus should be technical. I downloaded Symantec’s Application HA and decided to give it a spin, I already started documenting the installation of the ApplicationHA Console and the Guest Component but Mr Sloof beat me to it and documented his finding in the following two articles.
- ApplicationHA – Install and Configure
- The ApplicationHA Configuration Wizard – Monitoring SQL Server 2008
No need to repeat it in my opinion as Eric did an excellent job. I do want to point two things out and they are around the requirements/constraints of the product:
- Symantec ApplicationHA Console requires Windows Server 2008 or Windows Server 2008 R2.
- The Console provides the integration between vCenter and ApplicationHA from a UI perspective. An ApplicationHA tab will be added to the vSphere Client which can be used to configure and control ApplicationHA.
- A 64Bit Guest OS is required for the ApplicationHA Windows Guest Component.
- This is the actually component that enables application level protection.
This basically means that if you are primarily using 32Bit OS’s, like I for instance do in my homelab, it won’t work as the installer literally throws an error that the VM doesn’t meet the requirements. That is for now, as I bet that when demand grows Symantec will add support for 32Bit OSs.
So what is this ApplicationHA product?
Symantec ApplicationHA is an extension of VM / Application Monitoring. Symantec simplified Veritas Cluster Server (VCS) to enable application availability monitoring including of course responding to issues. Just to be absolutely clear, the foundation still is VCS based the unnecessary bits and pieces were taken out. Note that it is not a multi-node clustering solution like VCS itself but a single node solution.
The question remains how does it integrate with vCenter and more specifically with HA?
Lets start with the integration with vCenter. This is where the “ApplicationHA Console” comes into play. It basically adds a tab on a VM level that gives you the details of this VM in terms of ApplicationHA of course depending on the fact if you installed the Guest Component or not the Tab will display different info. Ultimately it should look as follows:
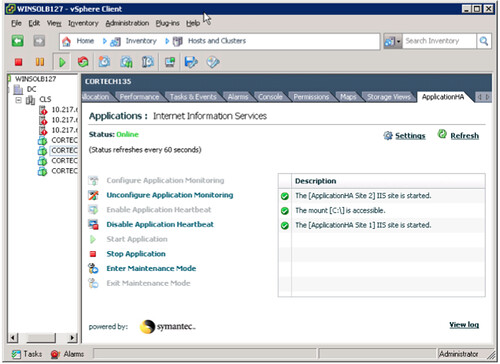
Now this example shows IIS being monitoring, but not only IIS also a disk mount. By the way, besides having a standard agent for IIS; ApplicationHA also includes an agent for MS SQL and MS Exchange. My primary focus for this article is Windows by of course Symantec also offers agents for Linux which includes Oracle, SAP and Weblogic. Just because your application is not included today it doesn’t mean you are out of luck. Symantec regularly updates the ApplicationHA Agent pack. However there is also a standard Guest Component which enables you to monitor standard services, mountpoints, processes and is what Symantec calls an Infrastructure Agent.
That brings me to the next point. From a GUI perspective it seems like there is a single component that monitors the state of your application. That is not the case, as stated above it can monitor the availability of services, process and much more. As stated this is what Symantec calls the Infrastructure Agent and yes it has multiple components. I have listed the most crucial agents below with a short description:
- Heartbeat Agent – The Heartbeat agent monitors the configured application service group.
- MountMonitor Agent – The MountMonitor agent monitors the mount path of the configured storage. It is independent of how the underlying storage is managed (whether SFW disk groups or LDM disks or any other storage management software). The mount path can be a drive letter or a folder mount.
- GenericService Agent – The GenericService agent brings services online, takes them offline, and monitors their status. A service is an application type that is supported by Windows, and conforms to the interface rules of the Service Control Manager (SCM).
- Process Agent – The Process agent brings processes online, takes them offline, and monitors their status. You can specify different executables for each process routine.
Each of these agents has very specific configuration attributes. An example for instance would be the “DelayBeforeAppFault” for the Heartbeat Agent. This specifies the number of seconds the agent must wait in case of an error before communicating application fault to VMware HA. I guess I just hit the nail on the head. The Heartbeat Agent is the agent that is responsible for communication with VMware HA. Basically it provides a means to trigger VMware HA to kick in when Symantec can not handle the issue with a restart of the service.
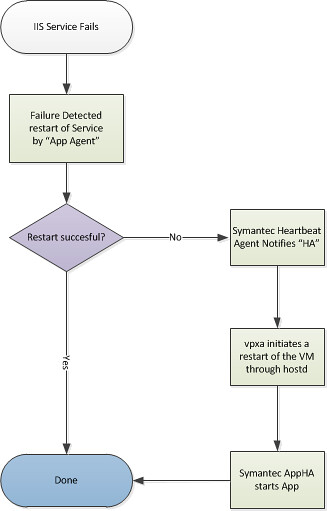
So what happens if an Application that has been configured for protection fails?
First Symantec ApplicationHA is triggered to try to get the Application up and running after the failure occurred by restarting the application. It should be noted that Symantec’s ApplicationHA is aware of dependencies and knows in which order services should be started or stopped. If however for whatever reason this fails for an “X” amount of times VMware HA will be asked to take action. (X is configurable by changing the config attribute “AppRestartAttempts”.) The action that HA takes will be a restart of the virtual machine.
But wait is it really VMware HA? With that meaning is it the good old “AAM” agent who is responsible for this action? No it isn’t. In this case both “vpxa” and “hostd” are responsible for the action taken. I guess visualizing the process will make it a bit easier to digest:
I hope this makes it a bit more clear on how the product works and how it integrates with VMware HA itself.
hi
I am a little bit concerned by the proliferation of agents installed on vms
“I hope this makes it a bit more clear on how the product works and how it integrates with VMware HA itself.”
What I get from this is that it does not integrate with VMware HA at all (which is not a bad thing). It uses other services and a daemon inside the VM to perform its tasks.
It is actually interfacing with VMwareHA. If ApplicationHA cannot handle application re-starts from within host, it informs VMwareHA to take action.
So in the end whats the benefit?
If you maintain your traditional monitoring you could integrate these to execute restart scripts like service scripts within the VM, and then if that fails initiate a restart of the VM using Power Shell.
I had a look at this at vForum in Sydney, the Symantec rep failed to be convincing, at the price they charge per VM it also appears to me at this time to be limited to only a few use cases if at all.
On the upside;
It’s monitoring out of band, I think. So a network failure will not cause an error elsewhere.
It does have some smarts around service dependencies that you don’t have to worry about.
Would be fairly simple to configure compared to a script, maybe ;-).
Anyone from Symantec care to comment about use cases?
Oh and thanks Duncan for another great Blog.
tell them that if they don’t do as you wish, you’ll become angry and use your magic
Thanks Duncan for sharing this.
Since it only uses 1 VM, one use cases that it does not cover (relative to cluster-ware) is Rolling Upgrade or Patch.
@Nathon I do agree as well.
You can also add to the fact that it performs some automation and integration to the vSphere suite. Central Management is a nice bonus and yea the time it takes to set this up could be less instead of having to write scripts and such. Thanks for sharing Duncan I cannot wait to see what other products come rolling out.
And the question is who monitors the Symantec Agents?
I guess VMware HA doesn’t 🙂
This product would certainly fit a case for sure, but I haven’t met one yet I could not get around with customer’s existing tools/monitors/procedures.
This is version 1.0 so I expect the product will mature even further.
Rgds,
Didier
Since it is based on top of Veritas Cluster Server(VCS), the agents themselves are monitored by VCS. VCS is a enterprise class high availability software and there are self protection mechanisms implemented within it.
a MoM should monitor the agents… 🙂
I have recently started a website, the information you provide on this web site has helped me tremendously. Thank you for all of your time & work. “It is no use saying, We are doing our best.’ You have got to succeed in doing what is necessary.” by Sir Winston Churchill.
Duncan,
Is it possible to use HA to restart the application on another VM if the application will not restart or is the only option to restart the VM and see if it will start.
We have a application that is not cluster aware one runs as a master, one as a replica. What I would like is to have the application started on the replica is the master fails for whatever reason