I had some difficulties scheduling guests the past weeks due to my travel schedule, and as a result, I figured I would try something new. In this episode, I go over the various things I announced at Explore and Explore on Tour in London, Paris, and Frankfurt. I talk about VCF Native S3 Object Storage, the enhancements we are planning for Disaster Recovery as well as Cyber Recovery, and I also briefly touch on vSAN on FC.
You can listen to my solo episode, episode 108, on Spotify (bit.ly/3MxRyZC), Apple Podcasts (bit.ly/4iEM5ML), or via the embedded player on Yellow-Bricks below.
If you like to hear more about vSAN ESA Global Deduplication, make sure to go to this blog on Yellow-Bricks, as it contains the links to the discussion Pete Koehler and I had on the show a while back. I also just published the demo I recorded for Explore on Youtube, make sure to watch that one!
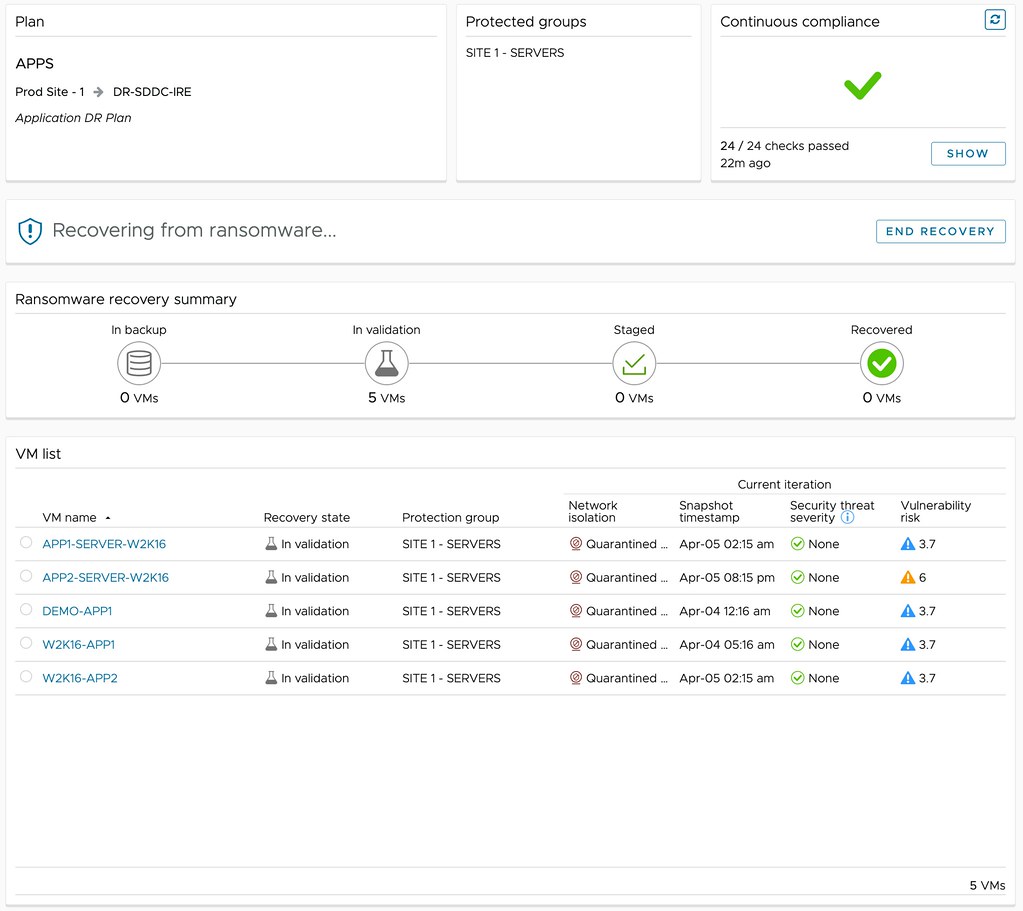
I also had Jatin Jindal on the show a month or two ago to discuss all Ransomware/Cyber Recovery enhancements in-depth. You can listen to that episode via Spotify (bit.ly/3IWQCwz), Apple (bit.ly/4o6YVoG), or via the embedded player on yellow-bricks.com!
 Last week a blog post was published on VMware’s Virtual Blocks blog on the topic of
Last week a blog post was published on VMware’s Virtual Blocks blog on the topic of